Secure in Public?
Your tired and tired of working in your office, so you head down to the nicest Starbucks in your area to get a coffee. The shop has got a few other people in it like you - waking up from a low point in the afternoon. You notice that several of the people have laptops, but there is a nice table near an outlet so you can plug in if you need it.
Still needing to get some work done, you bring your laptop and access their free WiFi there. While you are still waking up, you get onto Facebook to check what your friends are doing and do a little personal searching. You may even send out a tweet or two to see if you can get any of your friends to join you. All seems good as you settle into your work.
What you don't notice is the woman in the corner busy working on her laptop. She happens to be running Firefox with a new add-on called Firesheep. Firesheep can access the traffic on a public (meaning unencrypted) WiFi network. It doesn't take a highly skilled user to see the traffic that is passing through the network. The add-on grabs your Facebook, Twitter, and other passwords. It is also capable of grabbing all of unencrypted content that is sent across the network. This is independent of your Facebook privacy settings.
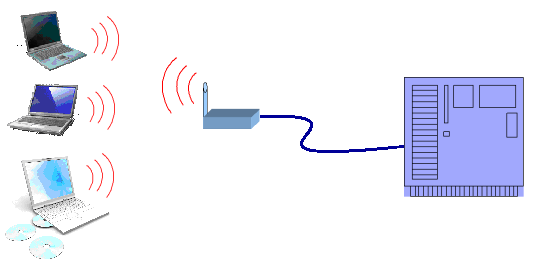
This is what is happening. Your laptop and the WiFi access point communicate via radio waves. The content is digital, but it is broadcast for anyone to pick up that is within range of the signal. The information is put into a particular protocol (format), but the protocol is public and widely known. Anyone can listen in. Once it reaches the access point, the signal travels by wire to the destination where it is processed and a response is generated. The response travels by wire until the access point, then it is broadcast for everyone to receive. The reason you receive the signal and process it is the WiFi protocol includes references to the two parties (your laptop and the access point) that are communicating.
But you say that you are legally protected from being intercepted by wiretapping laws. Well, perhaps, perhaps not. You are not protected if you use a speaker phone. The electronic portion of conversation is most likely protected, but anyone nearby can hear the entire conversation - and it isn't protected. You have chosen to broadcast (aurally) your conversation to all within hearing range.
There is another school of thought that states that when people are accessing sites they believe to be private, there is an expectation of privacy; independent of the openness of the signal from origination (your laptop) to the destination (the private web site). This line of reasoning is not held by a majority of legal experts; however, none of this is determine until argued in court or statutes are passed.
Even after this issues is legally resolved, it is still better to make sure that your private transactions are encrypted over all public WiFI access points.
For additional information:
- Is it legal to use Firesheep at Starbucks? from Network World
- Mozilla's Firefox
- Firesheep
